Macs have a reputation for being virus-proof, which can cause people to be lax about their security measures. While cybercriminals develop far less malware for Mac OS than Windows, these computers are still at risk. Here are warning signs to look out for from your end users:
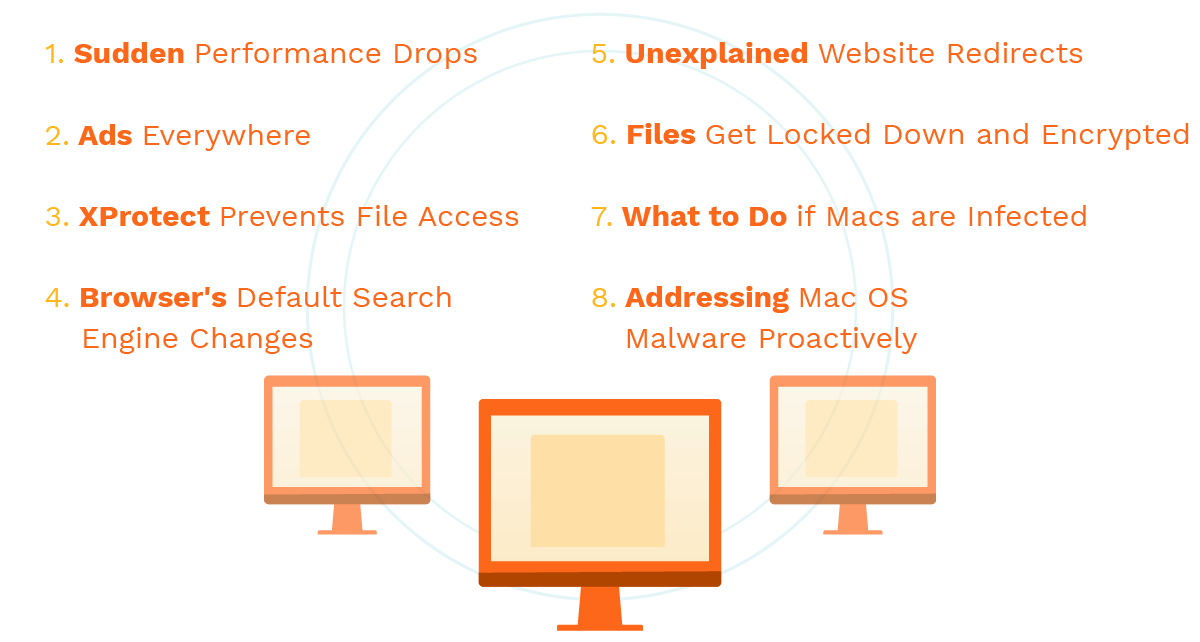
1. Sudden Performance Drops
Workstations that have never had issues suddenly run into performance problems. End users may complain that their systems are slow, applications are crashing, and input is sluggish. Malware can take up a lot of resources and interfere with normal operations, which leads to the performance degradation.
2. Ads Everywhere
Adware places advertising everywhere it can access, which can result in pop-up windows and browsers that are practically unusable due to these disruptions.
3. XProtect Prevents File Access
If XProtect detects malware in a file, it stops the end user from opening it. When you have multiple people reaching out to you about file access issues, take a look to see if malware is the root cause.

4. Browser's Default Search Engine Changes
Another adware related symptom is the web browser's default search engine getting switched. When the end user goes to search, they may end up using a site that's compromised by the cybercriminal. Trying to go back to the previous search engine may prove difficult, or that functionality could be entirely locked down.
5. Unexplained Website Redirects
Some malware intercepts web traffic and sends it to a different destination. The hacker may use this as part of a phishing attempt. They can attempt to get login information, security question answers, and other personal information.
6. Files Get Locked Down and Encrypted
Mac OS ransomware takes control of the computer and encrypts all of the files on that system (or the entire network). The end user can't access this data or normal system functions. The attacker demands a payment, typically in Bitcoins, for the encryption key. You may have a timer counting down until additional fees are requested or the data is deleted.
7. What to Do if Macs are Infected
If users start to send in tickets and requests with these warning signs, start investigating immediately. You don't want a virus to get a foothold on someone's workstation or for it to reach the rest of the network.
Anti-virus, anti-malware, and advanced threat detection solutions can identify and respond to this malicious software. Once you neutralize the immediate threat, it's time to look at Mac OS virus prevention.
8. Addressing Mac OS Malware Proactively
You can put several measures in place to reduce the Mac-based attack surfaces in your business network. Have staff members go through cybersecurity awareness training so they can help you identify these warning signs before an infection becomes a much larger problem.
Routine maintenance, such as scanning the systems for malware and applying the latest operating system and firmware updates, reduce the exploits that attackers use.
Macs may have fewer malware threats than Windows, but that doesn't mean that proper cybersecurity measures should be overlooked. Keep a sharp eye out for early warning signs to keep your organization safer.
Categories: Security, Network Security











