On Monday, June 17th, the Cybersecurity and Infrastructure Security Agency (CISA), a sub agency of the Department of Homeland Security, released a critical warning targeted towards Microsoft Windows users. This alert, which is only the third alert to be issued by the CISA in 2019, warns users of a potential malware threat, referred to as BlueKeep.
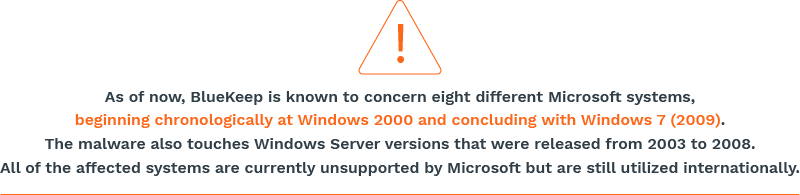
BlueKeep, also known as CVE-2019-0708, is a computer worm that was discovered in May 2019. Its origins are either unknown or have yet to be publicly released. However, the situation mirrors the WannaCry attacks that occurred in mid-May 2017, which have since been linked to North Korea.
Although the word “virus” is often used an all-encompassing term for malware, computer worms are equally, if not more, dangerous. A worm does not attach itself to a specific location or file, but instead, it enters many computers through a vulnerability on a shared network or operating system.
Unlike viruses, worms do not require human initiation to infect a device. Because of this, worms have the ability to replicate themselves and quickly spread to other computers. In the case of the BlueKeep worm, which affects international Microsoft systems, this worm has the potential to disrupt users worldwide.
According to the CISA alert, the BlueKeep worm has the potential ability to take control of an infected system by sending “specially crafted packets” to one of the previously listed operating systems. After successfully sending the packets, the worm would have the capacity to add “accounts with full user rights,” edit or delete data, and install programs.
If left untreated, we expect the attackers to begin exploiting the hacked data within the next few weeks. Luckily, Microsoft has issued a patch, that if installed, should protect systems from being infected. However, if left unpatched, upwards of a million machines are left vulnerable to the BlueKeep worm.
Unfortunately, the threat does not stop there. BlueKeep’s wormlike traits enable it to replicate itself and slither onto other devices via internal networks. A BlueKeep attack could use older Windows systems as a gateway to infiltrate many more computers. A breach of this scale would cause global devastation, similar to the WannaCry crisis.
To protect your business, it is imperative that you install the Microsoft patches. You can also protect your business by properly configuring your Remote Desktop Protocol by avoiding access to public internet, or disabling your RDP until the patches are installed.
Categories: Security, Cyber Security, Network Security










