Managed IT Services
End IT headaches with reliable, US-based support that ensures seamless operations.
.webp?width=472&height=487&name=Managed-IT%20(1).webp)
Discover the Unparalleled Advantage of a Dedicated IT Partner
Managed Services = Peace of Mind
Navigating the labyrinth of modern technology landscapes can be daunting. Without the necessary expertise and insights, the rapid evolution and the intertwined complexities they present can be overwhelming.
With a dedicated IT partner by your side, you can quickly sidestep potential downtime, optimize efficiency, and harness cutting-edge solutions tailored to your unique needs.
Let technology propel your business forward while ensuring agility, resilience, and security.

Optimize Operations & Accelerate Growth
Maximize Efficiency
Identify and eliminate operational inefficiencies, automate processes, and build on a solid tech foundation.
Enhance Profitability
Tailor your tech solutions to fit your unique needs, streamlining operations and boosting your bottom line.
Strategic Shift
We will move from reactive to proactive with strategic planning, leveraging our expertise to anticipate and meet future challenges head-on.
24/7 Support
Our US-based support team is available 24/7, ensuring your business operations never skip a beat.
Superior Tech Management
From cutting-edge hardware to enterprise-grade software, we manage, support, and maintain your tech infrastructure.
Compliance Simplified
Navigate the complex regulatory environment easily, keeping your business compliant and risk-free.
Unlock Potential
Partner with us and gain a virtual CIO dedicated to unlocking your business's full potential, helping you stay ahead of the curve.
Rapidly Respond to Security Threats
Office1 proactively monitors, identifies, evaluates, & resolves unexpected issues, ensuring you stay on track no matter the challenges.
Unlock the Key Benefits of Office1 Managed Services
We manage your IT while you focus on your business.
No two businesses are exactly alike. We closely examine your requirements, discuss present and future goals, and formulate a custom-tailored managed IT roadmap that perfectly fits your technological demands. We will provide ongoing technical support and maintenance to ensure your IT systems remain up-to-date and functioning optimally.

Step 1: Discover
We will explore the entire landscape of your IT infrastructure and operational needs, gaining valuable insights into existing systems and processes.

Step 2: Analyze
With comprehensive data in hand, our experts will conduct a meticulous analysis, identifying areas for improvement and untapped opportunities to enhance efficiency and productivity.

Step 3: Plan
Create a strategic roadmap that addresses your unique requirements, aligning business objectives with technology solutions to optimize performance and efficiency.

Step 4: Deliver
Implementing the meticulously crafted plan, we deploy cutting-edge solutions and technologies, ensuring a seamless integration that optimizes your IT infrastructure while minimizing disruptions.

Step 5: Manage & Optimize
Our dedicated team will continue to monitor and manage your IT ecosystem, proactively addressing potential issues and evolving needs to maintain peak performance and keep your company ahead of the curve while ensuring a secure and thriving technology environment.
Office1’s technical support and leadership team have always quickly and diligently responded to our tech concerns, malfunctions, and requests. They have assisted us in a variety of ways from everyday problem troubleshooting, in-person office tech set up, keeping us safe from malware, phishing attempts, and viruses, and even advocating on our behalf with tech vendors.
We are extremely grateful for the hard work, dedication, and attention we have received from the Office1 team and are happy to recommend them to any organization. They will truly give you peace of mind when it comes to your technology and that allows for your day-to-day operations to ultimately run better.
Our Services
Implement Firewalls, Web Filtering, Geo-Filtering, and Intrusion Detection
Office1 fortifies enterprise IT infrastructure, leveraging firewalls to block unauthorized traffic, web filtering to restrict access to malicious websites, and intrusion detection to identify and respond to security threats in real time. We can also limit access by location with geo-filtering.
Dark Web Monitoring for Compromised Accounts
We actively search the deep web for compromised credentials and alert businesses immediately. This swift and efficient approach allows organizations and individuals to act quickly and make the necessary changes to secure their accounts.
Monitor Email Tenants for Business Email Compromise, Users Granting Apps Access to Their Inbox, and Suspicious Inbox Rules
With our email security monitoring, you're always in control. We actively monitor email tenants for attempts to compromise business email accounts, unauthorized app access, and suspicious inbox rules.
Connection From Suspicious Locations and Impossible Travel
Leverage advanced anomaly detection and enhance login security. Office1 will monitor login attempts from unusual locations exhibiting impossible travel patterns in real-time. This approach helps organizations proactively identify and mitigate potential security threats.
Email Spam and Malware Filtering
Email security begins with filtering out spam and malware from your inbox. Office1 will provide your employees with a clutter-free and secure email experience by automatically quarantining spam messages and filtering out malware attachments before they reach your inbox.
Next-Gen Antivirus (NGAV)
Antivirus software still plays a critical role in enterprise security. Next-gen antivirus uses behavior-based detection and machine learning to enable advanced protection against zero-day threats and other sophisticated attacks, even if it has never seen them before.
End Point Detection and Response (EDR)
Empower your security team with a robust EDR solution. Through continuous monitoring of endpoints for anomalies, automated containment to isolate threats, and real-time insights and response capabilities, enterprises can minimize the impact of a potential security event.
Monitor for the Creation of New Services and New Users
Track users and service creation in real-time to quickly detect suspicious activity, including malware disguised as new services and unauthorized accounts. This approach helps contain insider threats and stop malware while maintaining complete network visibility.
Password Randomization
Office1's password randomization service helps secure businesses by generating complex, unique passwords for all your users. This approach eliminates the vulnerability of weak passwords that are known to allow threat actors into enterprise networks.
OS Patching
Outdated software puts your business at risk. Office1's automated OS patching service keeps enterprise devices safe by keeping them updated with the latest bug fixes while in-house IT teams focus on innovation.
Onsite and Offsite Backup
Office1's layered backup strategy ensures uptime and business continuity. Onsite backups enable rapid data recovery for everyday hiccups, while offsite storage protects data from natural disasters and security threats.
DNS Filtering for Suspect and Known Malicious Websites
Office1's DNS filtering services help block access to malicious websites harboring malware, ransomware, phishing scams, and inappropriate content. This proactive approach protects users from cyber threats while providing a safe and productive browsing experience.
Monitor Critical Services
Office1's real-time monitoring service proactively identifies performance anomalies and potential outages in critical applications and infrastructure. This approach helps IT teams address issues quickly, minimizing potential downtime while maintaining optimal productivity.
Monitor and Manage Antivirus Alerts
Continuously monitor and analyze antivirus alerts to distinguish real threats from false positives and act quickly to isolate, neutralize, and contain identified threats. Act on alerts as outlined in the Incident Response Plan.
Backup Monitoring and Testing
Leveraging automated tools to verify backup integrity and functionality continuously, Office1 can reduce the risk of silent failures, ensure data recovery, and minimize downtime when disaster strikes.
LOB Application Support
Office1's LOB experts handle everything from troubleshooting issues to ensuring compatibility with new technologies. This approach ensures that critical line-of-business applications are continuously optimized for peak performance.
Program Network Switches
Office1 configures and implements VLANs, QoS, and port security to optimize traffic flow, prioritize critical applications, and protect enterprise networks from unauthorized access.
Manage, Monitor, and Program Wireless Access Points
Office1 programs, monitors, and manages wireless access points to ensure accessibility and security. Our experts configure and secure guest networks, encrypt communications and provide optimal coverage and performance for guest and business traffic.
Plan, Implement and Manage Battery Backups
Power through disruptions with Office1's expert backup solutions. We ensure business continuity by planning, implementing, and managing reliable battery backups for critical systems. Take advantage of uninterrupted operation during power outages.
Implement and Manage Site-to-Site and User-to-Site VPN
Collaborate from anywhere securely while we implement and manage site-to-site and user-to-site VPNs. These encrypted connections facilitate seamless collaboration without compromising security.
Phishing Test
Basic phishing tests aren't enough to protect your business from AI-powered cyberattacks. Office1 offers advanced simulations that mimic real-world social engineering attacks to keep staff alert.
Cyber Security Training
As humans remain the weakest link, regular cybersecurity training is critical to mitigate the risk of a data breach. We help employees learn and stay alert to the latest threats and best practices, equipping them to recognize and defend against cyberattacks.
End-User Support
Streamline your IT operations with Office1's End-User Support. Whether it's a password reset, expert Microsoft Office support, seamless approved software installations, or remote hardware fixes, we've got you covered.
Employee Onboarding/Offboarding
Simplify the process of onboarding new hires and offboarding recent departures. Office1 helps minimize the burden on in-house IT teams by handling user provisioning, access control, and device setup for a smooth start and secure exit.
Compliance Management
Office1's Compliance Management service takes the headache out of navigating the complexities of evolving regulatory requirements. Focus on growing your business while we handle assessments, gap analysis, and ongoing monitoring.
Incident Response Planning
Office1's Incident Response Planning service helps businesses develop a robust strategy to quickly contain and recover from a cyberattack. This approach minimizes the risk of potential downtime, regulatory fines, and reputational damage.
Quarterly Business Reviews
Conducting a business review at the end of each quarter keeps us on the same page about your IT requirements. Our consultants will review progress, identify evolving threats, and tailor our services to optimize productivity while fortifying enterprise infrastructure.
Technology Roadmap and Implementation Planning
We will work closely with you to develop a strategic technology roadmap, outlining both business and IT goals and the roadmap to get you there. This approach ensures a smooth transition and maximizes the value of your IT investments.

A Certified Managed Services Provider
Our MSP program follows established industry guidelines and much more. As a certified managed IT service provider, we will prioritize and implement the most appropriate IT solutions to ensure business continuity and compliance.










Revolutionizing IT: The Critical Need
for Environment Optimization
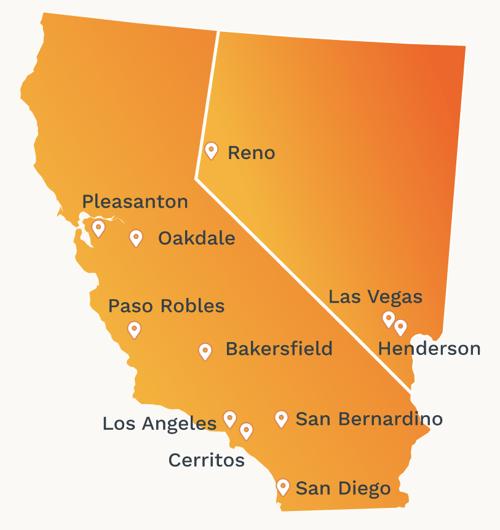
Locations
In California and Nevada, we have technicians who are ready to help you solve your IT issues. Whether you prefer to work remotely or meet in person, our team can accommodate your preference.


.webp?width=767&height=401&name=Setting-Up-IT-Strategy_767%20(1).webp)





